By default, Apple devices are moderately secure.
For those that are interested, here is a link to its Security Whitepaper (currently dated 2015, and for iOS1 8.3 or later). Its not always easy to find where on the line between security and convenience you want to be (and that doesn’t address the issue of changing your mind as new things happen, or you discover new ways of doing things). This article will cover a number of things you can do to improve the physical security of your device. Some of this will also apply to an iPod Touch, or an iPad.
Settings → Touch ID & Passcode
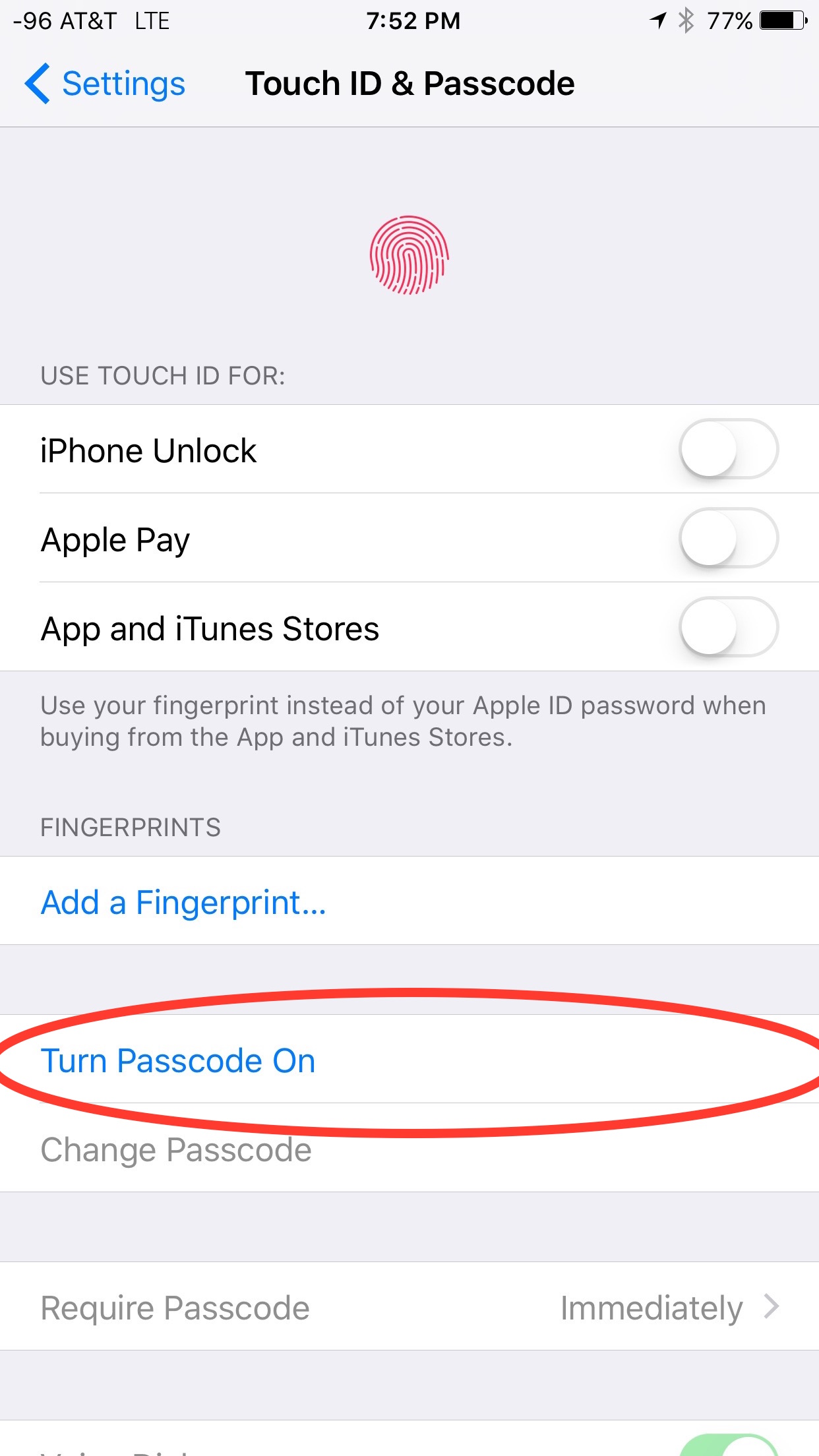
Under Settings → Touch ID & Passcode, we find the ‘Turn Passcode On’ settings:
Enable passcode
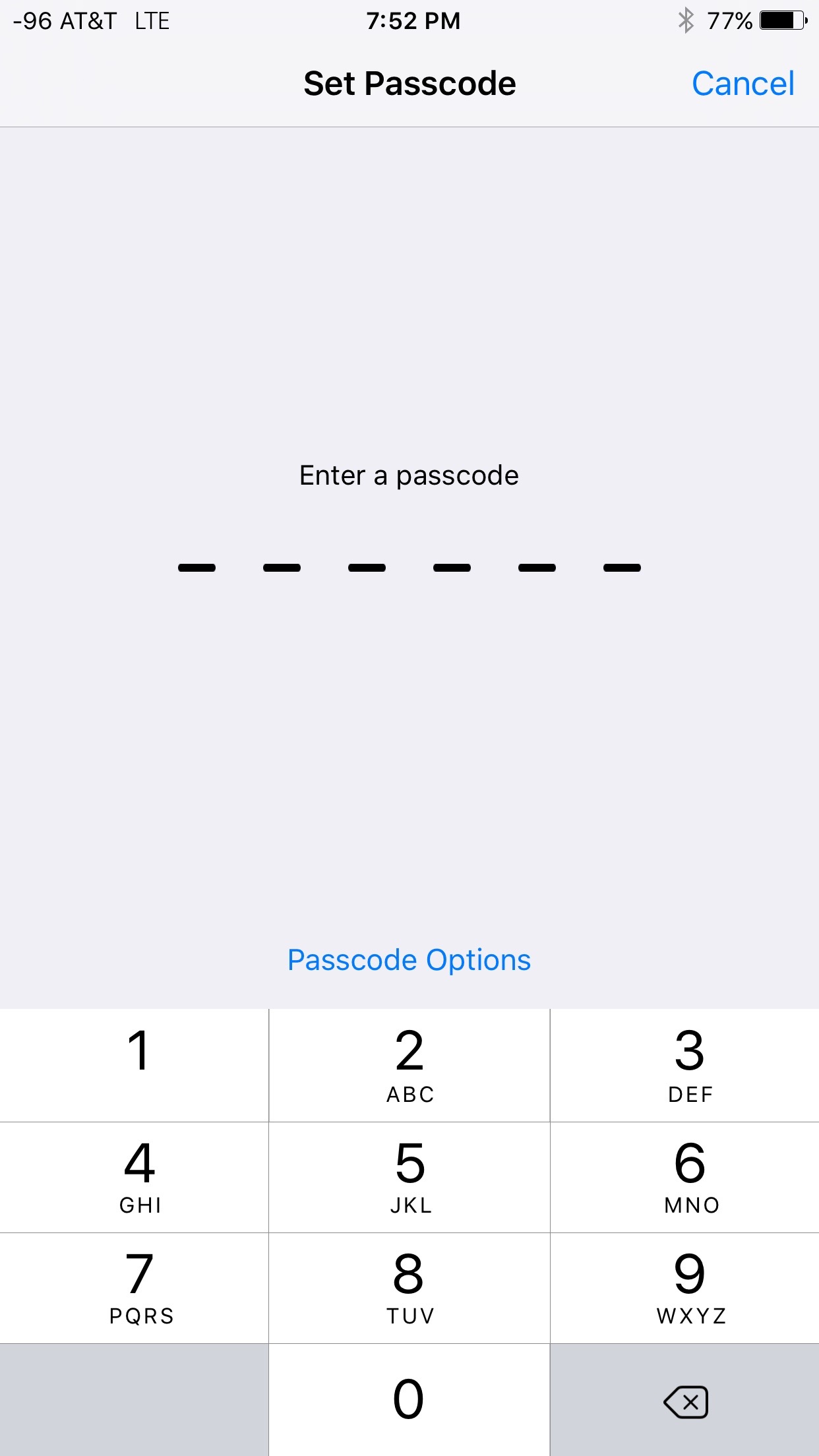
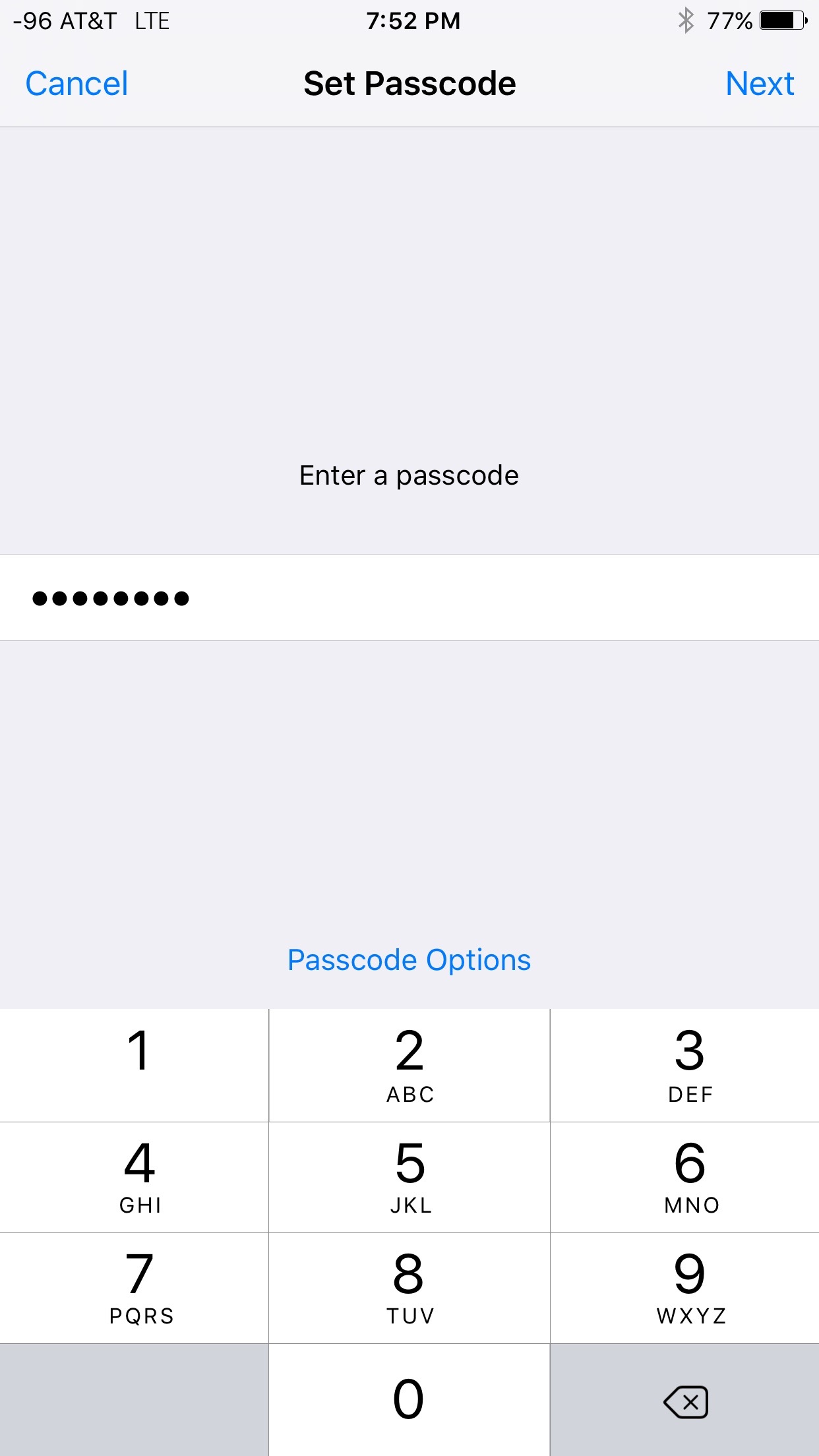
If you didn’t do this when you first setup the phone, you should do it now. After a bit of (real world) testing, I’ve concluded that a traditional password can be too complicated to enter on the lock screen under any kind of short time duration (This isn’t an issue for a normal cell call because Apple lets you accept the call from the lock screen, but VoIP applications don’t have that privilege, so apps like Groundwire or Silent Phone2 will stop ringing by the time you enter a complex password). That said, a traditional 4 digit PIN is certainly not long enough. Fortunately, Apple thought this through and provided the option of a long numeric PIN code (something that is longer than 4 digits). That’s easy to enter in a time crunch, but long enough its not practical for guessing. There are many numerical sequences that you could use. Some examples are ‘1, 3, 6, 10, 15, 21’ (Triangular numbers, if you start with one dot, add another row, you have 3, add another row, you have 6, etc), Pi (3.1415926), e (2.7182818). The passcode is what controls how difficult the phone is to get in to. It also unlocks other capabilities (discussed later). Choose a good passcode that you will be able to remember.
| Passcode | Passcode Options |
|---|---|
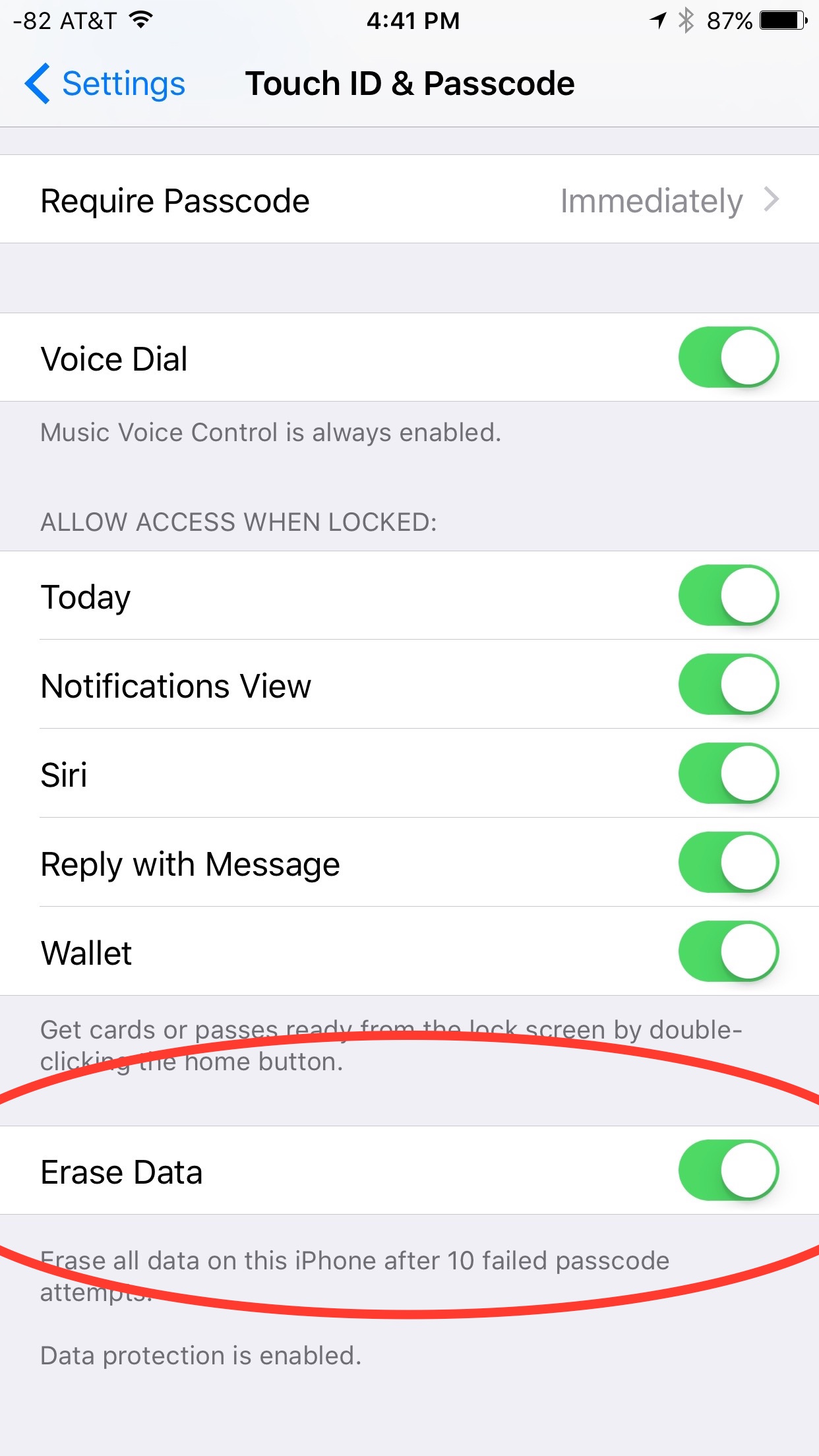
Lock screen
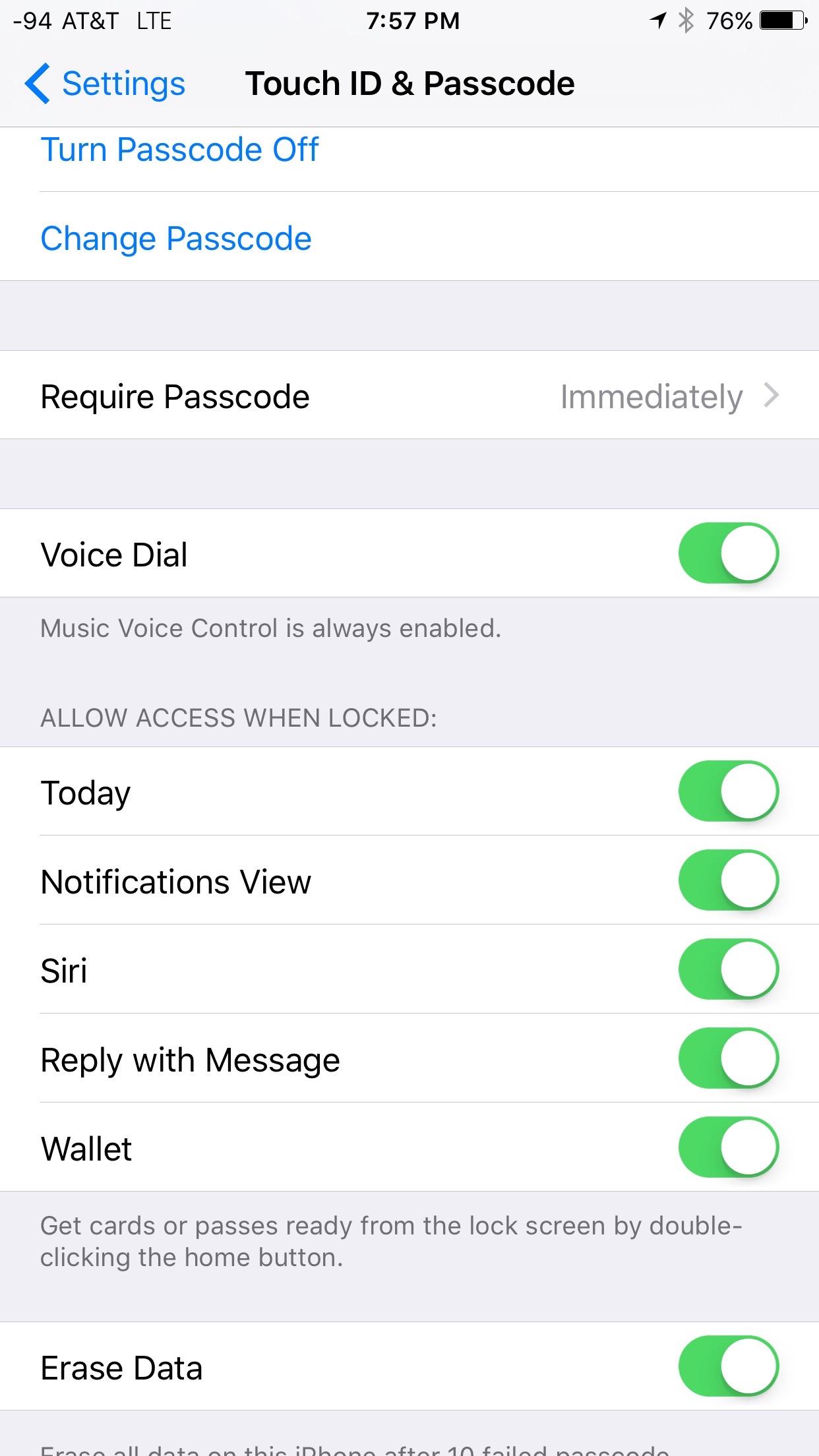
After creating a passcode, we can choose what we want to show up on the lock screen. This is important because it can tell a 3rd party information about you with out having to actually get into your phone. Things like missed calls, text messages (including reply to message), or access to Siri (which could allow them to call or send text messages to anybody in your contact list).
| Before | After |
|---|---|
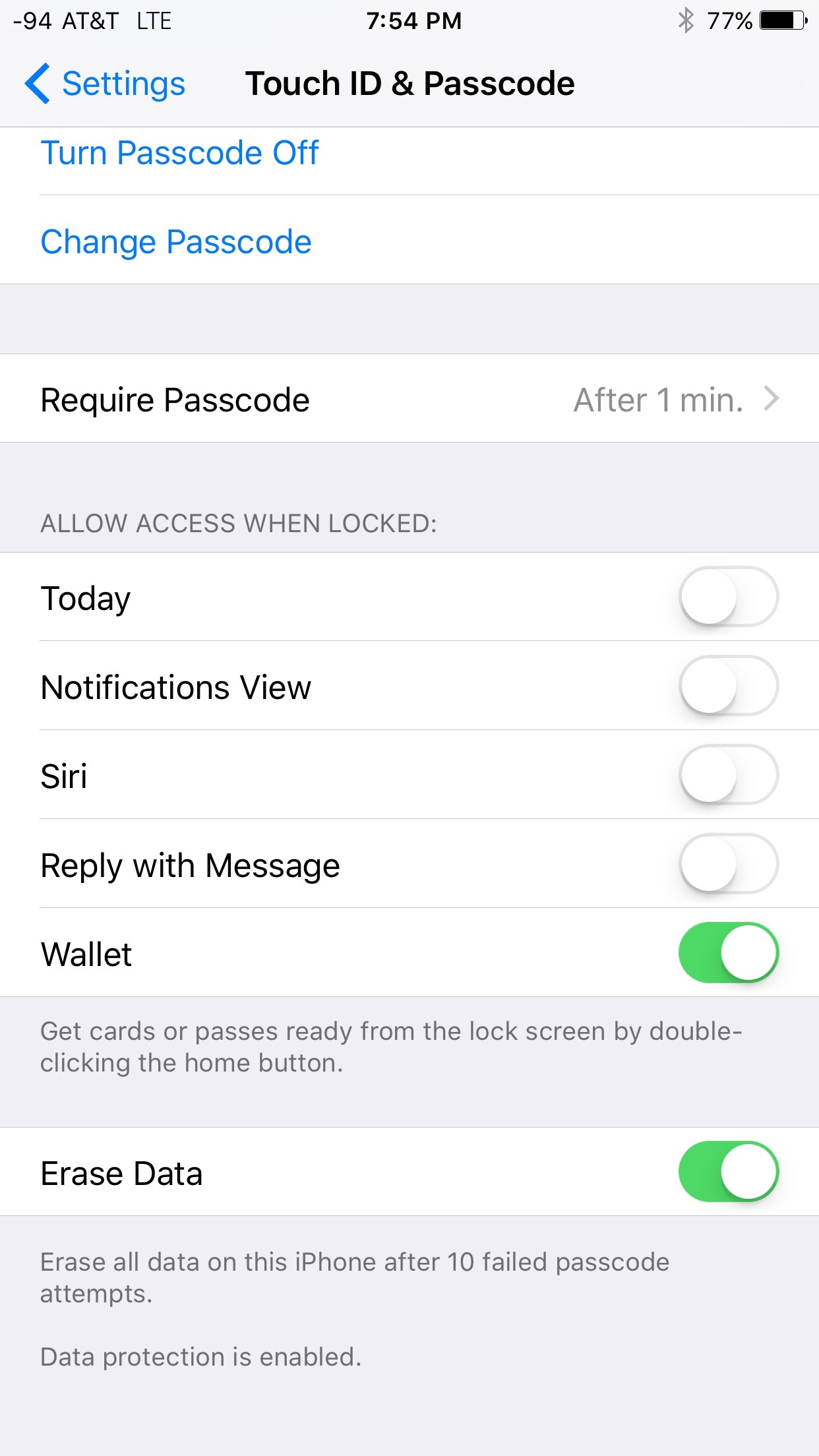
Enable wipe after failed login
Apple offers the ability to automatically have the phone wipe itself after 10 failed login attempts (password or passcode). Provided you don’t hand your phone to people who will constantly try to login to your phone (kids?), enabling this is a good idea. You can find this setting under: Settings → Touch ID & Passcode. When testing this out, simply creating a passcode caused this to be enabled, so you may not actually have to do anything for this.
Touch ID
If you have an iPhone 5S or newer, you can (optionally) take advantage of the fingerprint scanner built-in to the home button (Apple calls this Touch ID). Its worth mentioning that Touch ID doesn’t bypass the passcode. When you boot your phone, or go 48hrs (or longer), the phone will require you to enter the passcode. The passcode unlocks the ability for the Touch ID to unlock the phone, approve purchases (and app installs), and Apple Pay. if you aren’t comfortable using it, leave it off.
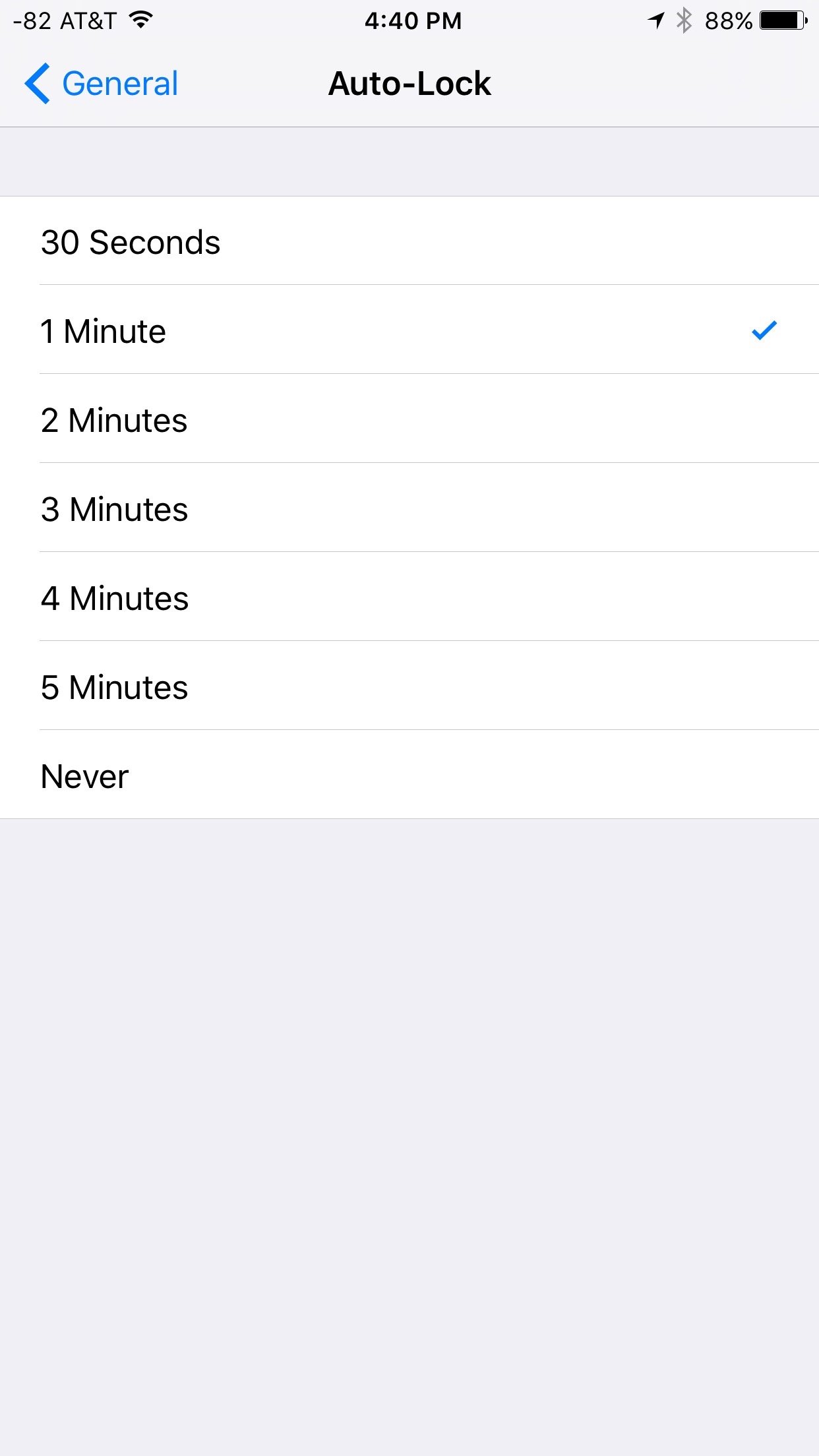
Automatically locking the device
Devices should be setup to automatically lock when you’re not using them. This will help keep other people from being able to pick up your phone and use if when you set it down. I have my phone set to lock after 1min. You can configure the auto-locking settings under: Settings → General → Auto-lock
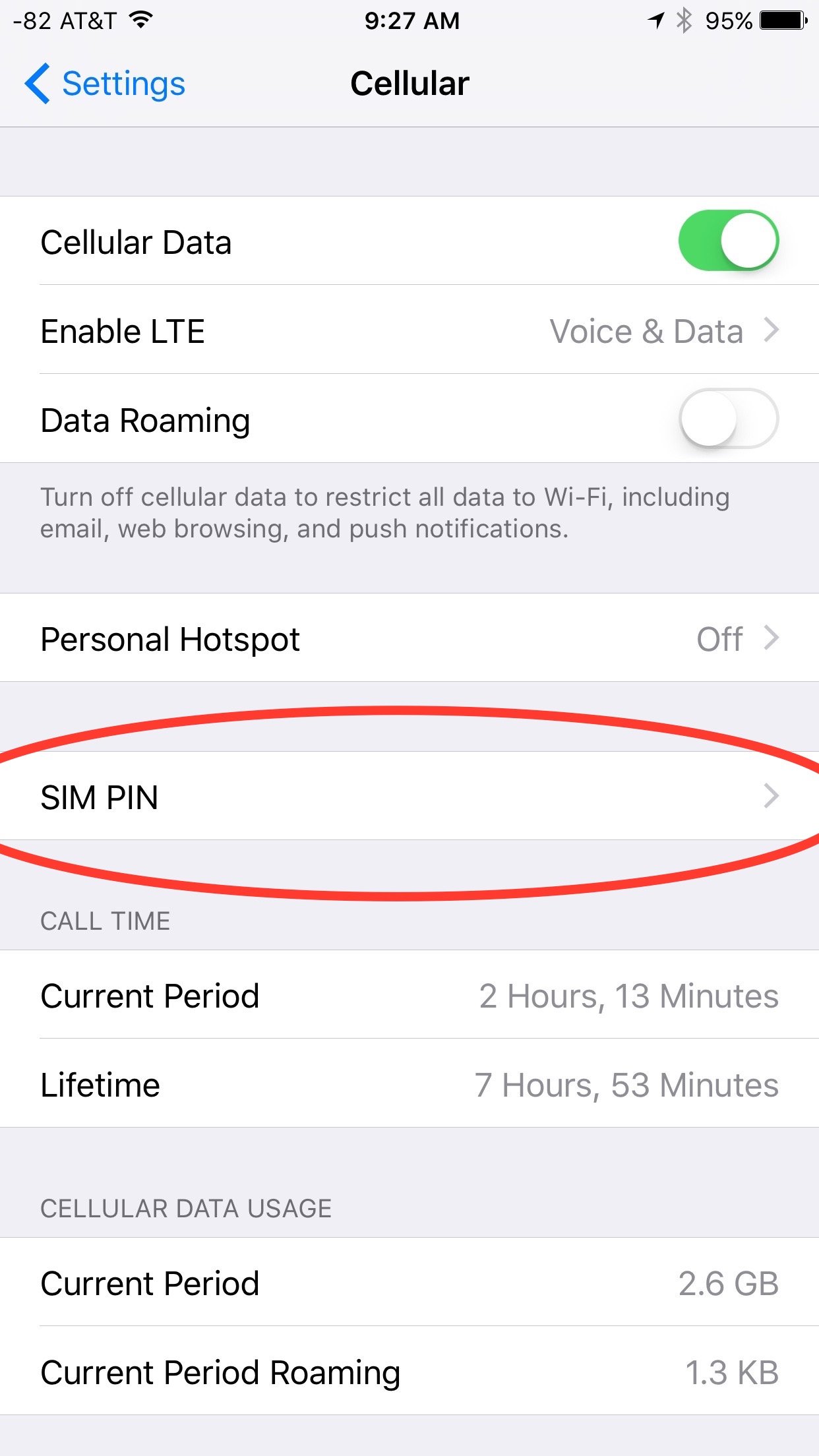
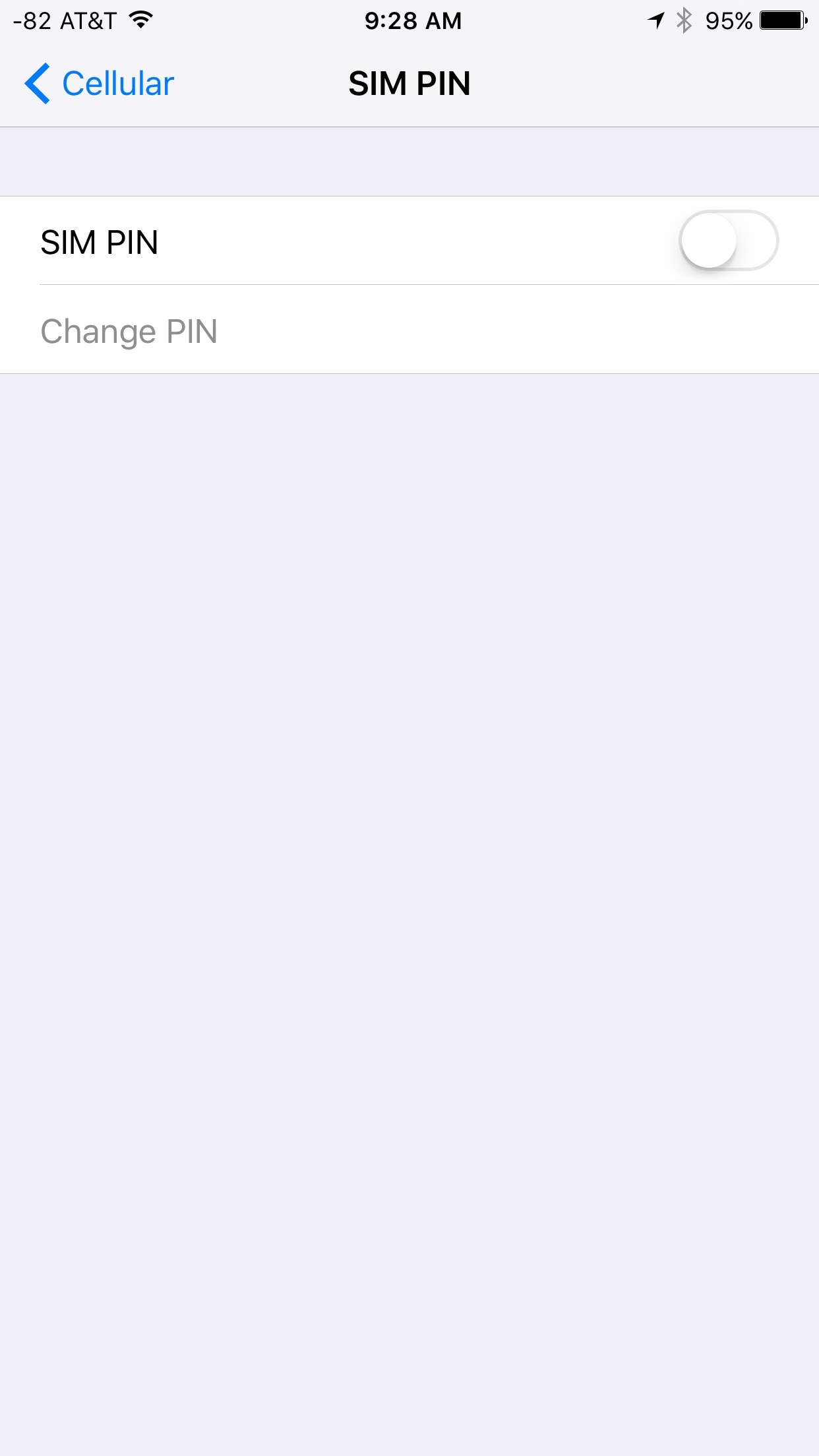
SIM Password
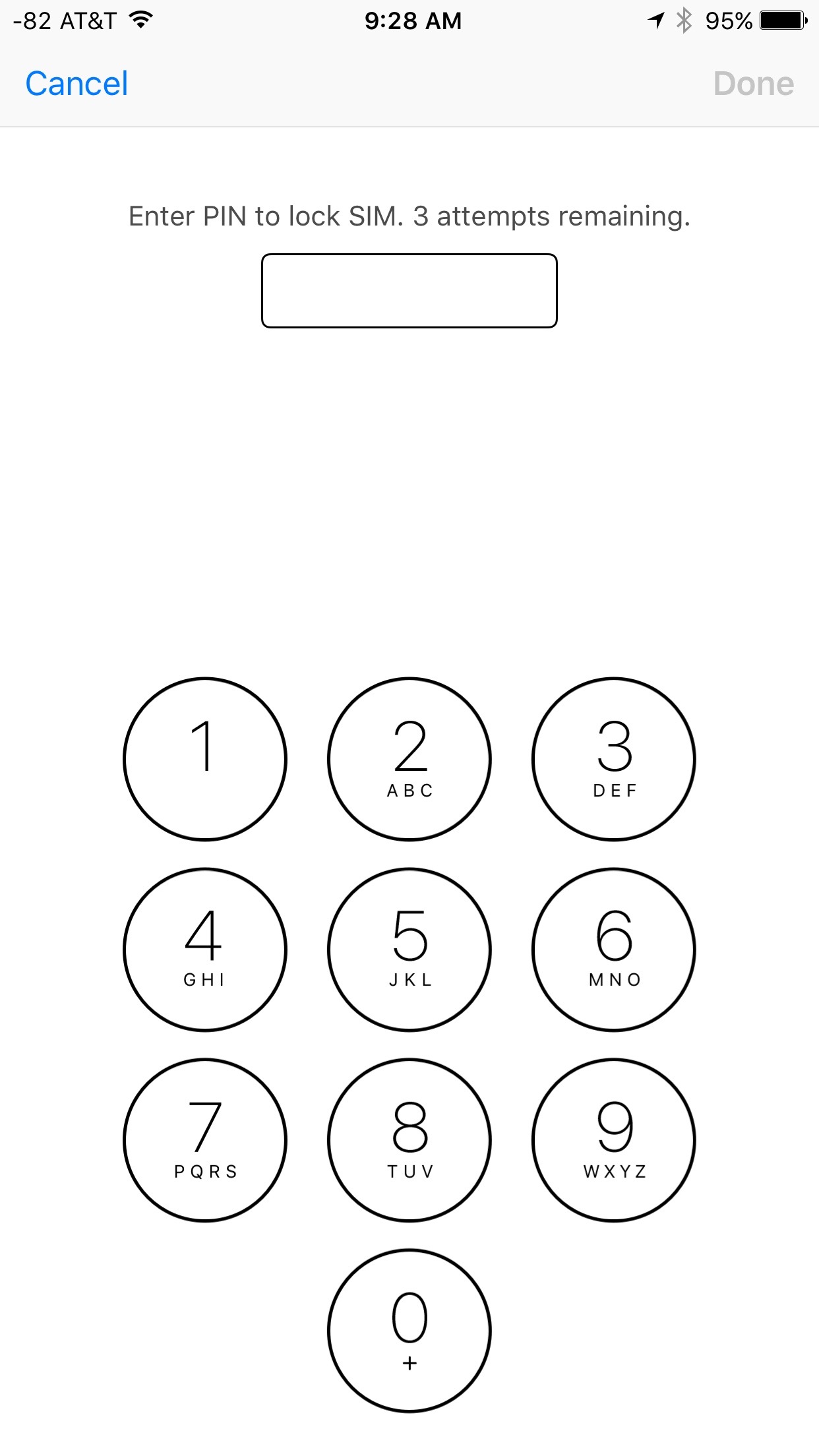
If you enable this feature on, your iPhone will require you to type in a four-digit passcode whenever you turn on the phone (to unlock the SIM3). This will prevent someone from making calls with your SIM3 in your iPhone (provided its not already turned on), or removing your SIM3 and using it in another phone. You can find the SIM3 Password under Settings → Cellular → SIM3 PIN
-
Enter the Current Password (for AT&T, the default is 1111. For other carriers check here )
-
Enter the New Password, a 4-digit passcode that you can remember; re-enter it to confirm.
The next time you turn on your iPhone you will be prompted to unlock your SIM3. If you forget your PIN, you will need to contact your carrier to unlock the SIM3 with a PUK4 code. If the PUK4 code is entered incorrectly too many times, the SIM3 will be blocked and you’ll have to get a new one.
Password Manager
If you’re going to be accessing and/or creating passwords on your iPhone, you should have a password manager. Many password managers are capable of integrating with desktop apps (with various methods of synchronizing). 2 examples are 1Password , and Lastpass . Both of these products are capable of keeping data in sync with a desktop app, generating and remembering passwords, and more.
Charging your iPhone
iPhone’s charge like many devices, via USB5. In addition to power, USB5 offers data capabilities. A malicious actor could reconfigure a USB5 port to try to hack your device. Don’t plug your phone into USB5 sockets you don’t know are safe. If you are in doubt, bring your apple power adapter. Alternatively, you can look at Portapow 6. They offer inline USB5 adapters that disable the data pins, resulting in only power coming across the cable.
Footnotes & References
-
iOS (originally iPhone OS) is a mobile operating system created and developed by Apple Inc. and distributed exclusively for Apple hardware. It is the operating system that presently powers many of the company’s mobile devices, including the iPhone, iPad, and iPod touch. - Wikipedia ↩︎
-
Silent Circle is an encrypted communications firm based in Geneva, Switzerland. Silent Circle provides multiplatform secure communication services for mobile devices and desktop. Launched October 16, 2012, the company operates under a subscription business model. The company uses open source peer-reviewed encryption. The source code of Silent Phone and Silent Text are available on GitHub under proprietary software licenses. - Wikipedia ↩︎
-
A subscriber identity module or subscriber identification module (SIM) is an integrated circuit chip that is intended to securely store the international mobile subscriber identity (IMSI) number and its related key, which are used to identify and authenticate subscribers on mobile telephony devices (such as mobile phones and computers). It is also possible to store contacts on many SIM cards. SIM cards are always used on GSM phones; for CDMA phones, they are only needed for newer LTE-capable handsets. SIM3 cards can also be used in satellite phones. - Wikipedia ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎ ↩︎
-
A personal unblocking code (PUC), also known as a PIN unlock key (PUK), is used in 3GPP mobile phones to reset a personal identification number (PIN) that has been lost or forgotten. - Wikipedia ↩︎ ↩︎
-
USB, short for Universal Serial Bus, is an industry standard developed in the mid-1990s that defines the cables, connectors and communications protocols used in a bus for connection, communication, and power supply between computers and electronic devices. - Wikipedia ↩︎ ↩︎ ↩︎ ↩︎ ↩︎
-
Blocks data transfer - your device will not go into ‘data transfer’ mode if connected to a computer, so you can use a computer just like a mains charger. This also prevents data hacking and any risk of viruses being loaded onto your device when charging from an unknown/public usb socket. - Portapow website ↩︎



Comments